Connecting to Hive with DBeaver using Kerberos Authentication
0) Install DBeaver
You can find installation instructions here
1) Download the latest drivers
You can find the latest drivers on the Cloudera website
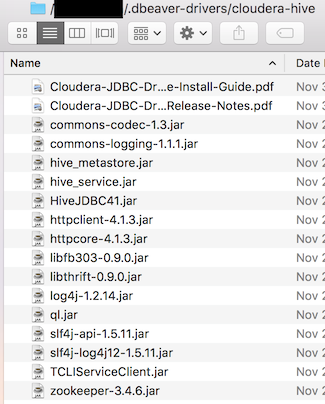
2) Create a folder to store the drivers
mkdir ~/.dbeaver-drivers/cloudera-hive/
3) Extract driver jars and move to the folder we made earlier
4) Create a New Driver in DBeaver
- Navigate to
Database > Driver Manager > New - Add all the files from
~/.dbeaver-drivers/cloudera-hive/ - Driver name:
Hive-Cloudera(for labeling only) - Class name:
com.cloudera.hive.jdbc41.HS2Driver(at the time of this writing) - Default port:
10000 - URL template:
jdbc:hive2://{host}:{port}/{database};AuthMech=1;KrbRealm=FOO.BAR;KrbHostFQDN={server}; KrbServiceName=hive;KrbAuthType=2- Note you need to change
FOO.BARto match your krb5.conf settings
- Note you need to change
5) Create a New Connection
- In the menu bar Navigate to
Database > New Connection - Select Hive-Cloudera
- Fill in the appropriate values for host & database (I set database to default)
- Set server to be your KrbHostFQDN
- Leave your user name & password blank
- Test connection
- Press next, next, & change the name of this connection as you see fit
- Press finish
Congrats you’ve successfully connected to hive using kerberos authentication!
6) Troubleshooting
If you are receiving [Cloudera][HiveJDBCDriver](500168) Error creating login context using ticket cache: Unable to obtain Principal Name for authentication make sure to check the following
- Ensure that you have the latest cryptography libraries installed
- Java 9 includes these libraries by default
- That you’ve configured your
/etc/krb5.confsuccessfully- If you’ve done this correctly you should be able to run
kinitin terminal and create a ticket without issue
- If you’ve done this correctly you should be able to run
For Windows adding the following lines to your dbeaver.ini may be necessary as well
-Djava.security.krb5.conf=c:\kerberos\krb5.ini- note: this is the windows equivalent of
/etc/krb5.conf
- note: this is the windows equivalent of
-Djava.security.auth.login.config=c:\kerberos\jaas.confsuccess has also been reported with the following jaas.conf file & keytab usage
Client { com.sun.security.auth.module.Krb5LoginModule required debug=true doNotPrompt=true useKeyTab=true keyTab="C:\Users\{user}\krb5cc_{user}" useTicketCache=true renewTGT=true principal="{user}@FOO.BAR" ; };